Find Vulnerabilities
Before Attackers Do.
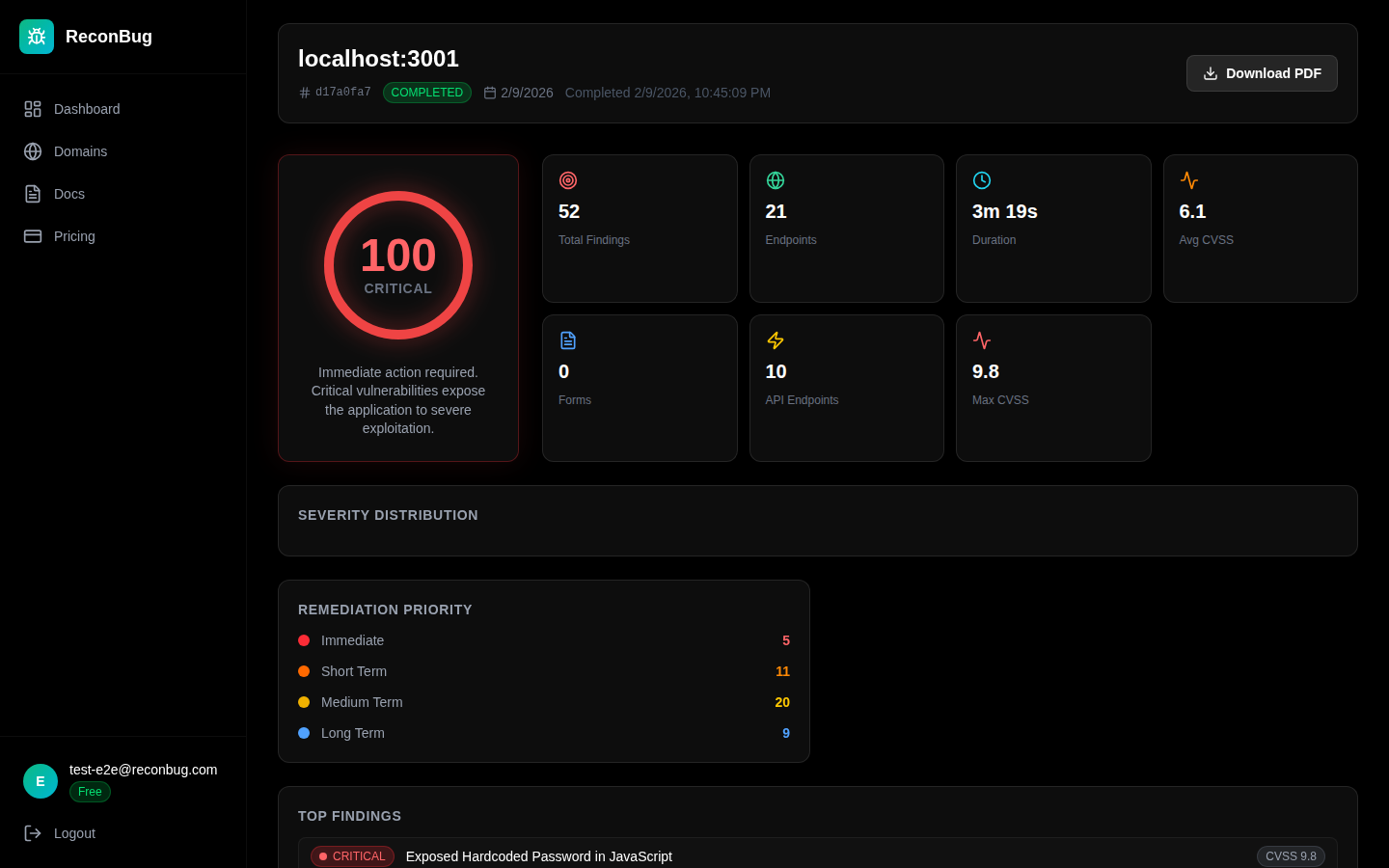
AI-powered OWASP Top 10 scanning that doesn't just find vulnerabilities, it proves they're exploitable with real attack chains. Deep security testing for modern web applications.
Launching soon. Be the first to know.